Hackers are currently using Microsoft OneNote attachments to spread malware in phishing campaigns. So users should not only be interested in Excel and Word files from unknown sources.
phishingUnfortunately, campaigns where mass emails are sent with malicious attachments are not uncommon. Cybercriminals have been willing to victimize this scam for years. Therefore, it should be normal now for most Internet users not to open Word or Excel files sent by unknown senders. But you shouldn’t just be wary of these two file formats, because hackers are always looking for new ways to protect your files malware to be published. Especially after Microsoft finally deactivated macros in Office documents by default in July last year.
Since then, security researchers have noticed attempts by cybercriminals to use different file formats, such as ISO images or password-protected Zip files. By using these two file formats, attackers also took advantage of the vulnerabilities they were able to exploit. However, both are now closed – and so hackers are once again looking for a suitable file format to spread their malware.
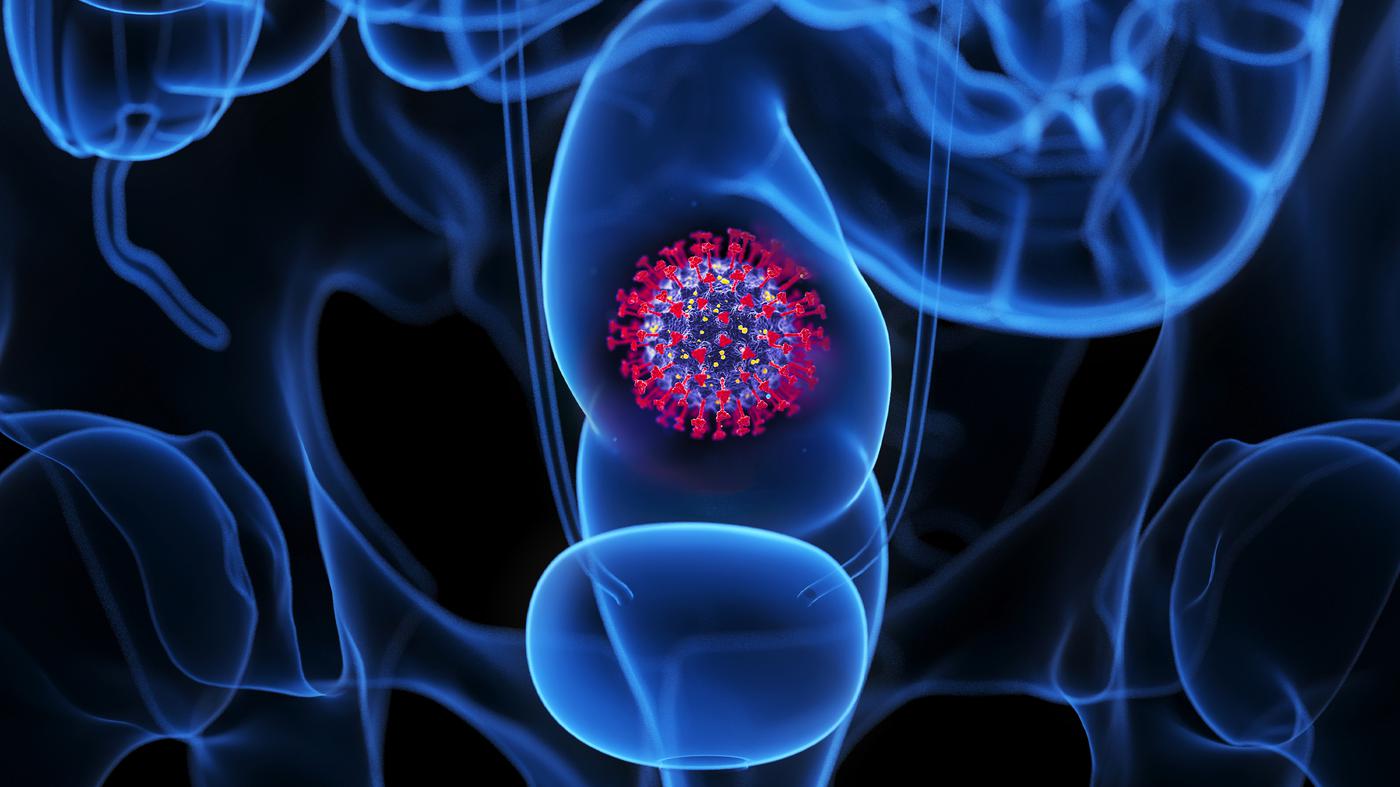
They also found what they were looking for Microsoft: Since December last year, infected OneNote attachments have been sent more and more often. This is a free application that is included with both Microsoft Office 2019 and Microsoft 365 It is included and acts as an electronic notebook. For attackers, this has the advantage that practically any user can open the attachment, even if they don’t use OneNote themselves. In one example described by BleepingComputer, the phishing message appeared to be a DHL shipping notice, but fake invoices, bank transfer forms, mechanical drawings, and shipping documents were noted.
Since OneNote, unlike Word and Excel, does not support macros in which criminals can hide their malware, the malware is now hidden in an attachment in what is called a notebook. When the user clicks on it, the attachment opens. These are usually malicious VBS files that automatically run a script that downloads and installs malware. However, visually, the attachments looked like the file icon in OneNote, so the hackers placed a large bar saying “Double-click to view file” over the listed VBS attachments to hide them. If you move them, malicious files become visible. However, if you simply click anywhere on the image file disguised as a button, there is a risk that you will get and open one of the files hidden behind it.
At this point, Microsoft has already installed a warning indicating that running the specified file may cause damage. However, experience has shown that many users simply click OK in this window – then the script is executed and two files are downloaded. The first is actually the OneNote document you expected. The second, however, is malware installed in the background, such as Remote Access Trojans (RAT) such as XWorm or Quasar.
Despite the new file format used, almost nothing has changed in terms of safeguards against such attacks. You should simply not open files from unknown sources. If this cannot be avoided, you should take the warnings from your computer seriously.
www.8com.de

“Subtly charming coffee scholar. General zombie junkie. Introvert. Alcohol nerd. Travel lover. Twitter specialist. Freelance student.”





More Stories
NASA receives the message via a laser beam from a distance of 226 million kilometers
Upgrade using 20 GPUs and 20 CPUs in testing [Update 3]
Adrenalin Edition 24.4.1: When the Manor Lords arrive tomorrow, the driver will be ready