The PrintNightmare vulnerability allows attackers under certain circumstances to execute malicious code
[datensicherheit.de, 12.07.2021] “As reported by many news portals, Microsoft’s print spooler service is vulnerable to a serious vulnerability (CVE-2021-34527)”Stephen Molls, “RVP, Risk & Security” at Tanium, mentioned in his current statement. This vulnerability enables attackers under certain circumstances to execute malicious code with system rights and thus To put the system at risk. Molls erläutert: “In order to successfully exploit the vulnerability, the attacker must have at least user/authentication rights.” Unfortunately, there is now at least one known case in which this vulnerability was effectively exploited – which turned out to be in the media: This case concerns the District Administration in the county of Anhalt-Butterfeld in Saxony-Anhalt, where this vulnerability was used to distribute ransomware. This malware eventually led to a complete IT failure.”
Photo: Tani
Stephen Molls: Companies should know which services are currently running and be able to stop them immediately!
The PrintNightmare icon got online by mistake
The exploit code for this vulnerability is “Accidentally” got on the internet, “When Sangfor’s Security Researchers Prepare for Black Hat 2021”. Attacker development efforts were minimal and attacks could be carried out Implemented with tools already available has become.
Microsoft has an official on July 7, 2021 emergency correction published for this exploit, “Which, as it turned out shortly thereafter, does not yet provide adequate protection against an attack in some configurations”.
PrintNightmare Exploit Protection: Deactivate the Print Spooler
So some companies still have another option Instead of helping yourself with ‘workarounds’, for example by deactivating the print spooler service. In view of its functionality, however, this is the problem of such a service Essential for all printing operations is being:
“It is not only necessary for the smooth operation of physical printers, but also for PDF documents, XPS and OneNote.” For server operating systems such as “Microsoft Server 2016”, there are no patches, they must be present Just follow the next few days.
PrintNightmare warns companies not to roll out and install necessary patches
It is especially important now for companies to have an overview of their endpoints, i.e. their patch cases, and be able to do so on the spot. “Put up and install the necessary patches”. An endpoint management solution can help with such updates Fast and resource-saving to circulate.
In addition, it can isolate unpatched endpoints so that if they are compromised No horizontal movements are possible in the company network شبكة is being. “If a patch is currently not an alternative, it is critical that companies know what services are currently running and be able to stop them immediately.”, betont Molls.
More information on the topic:
golem.de, Anna Beasley 08.07.2021
Anhalt Bitterfield: Ransomware paralyzes region management
Hayes Online08.07.2021
Windows Update Incomplete: Security Researchers Bypass PrintNightmare Patch
golem.de, Anna Beasley, 07.07.2021
First fixes for a Windows security hole / problem with the print spooler in Windows that allows attackers to execute code remotely. The first patches are available, but not for everything yet
datensicherheit.de, 02.07.2021
PrintNightmare: Malwarebytes Briefly Comments on a Vulnerability in Microsoft Windows / Advice from Malwarebytes Administrators

“Subtly charming coffee scholar. General zombie junkie. Introvert. Alcohol nerd. Travel lover. Twitter specialist. Freelance student.”






More Stories
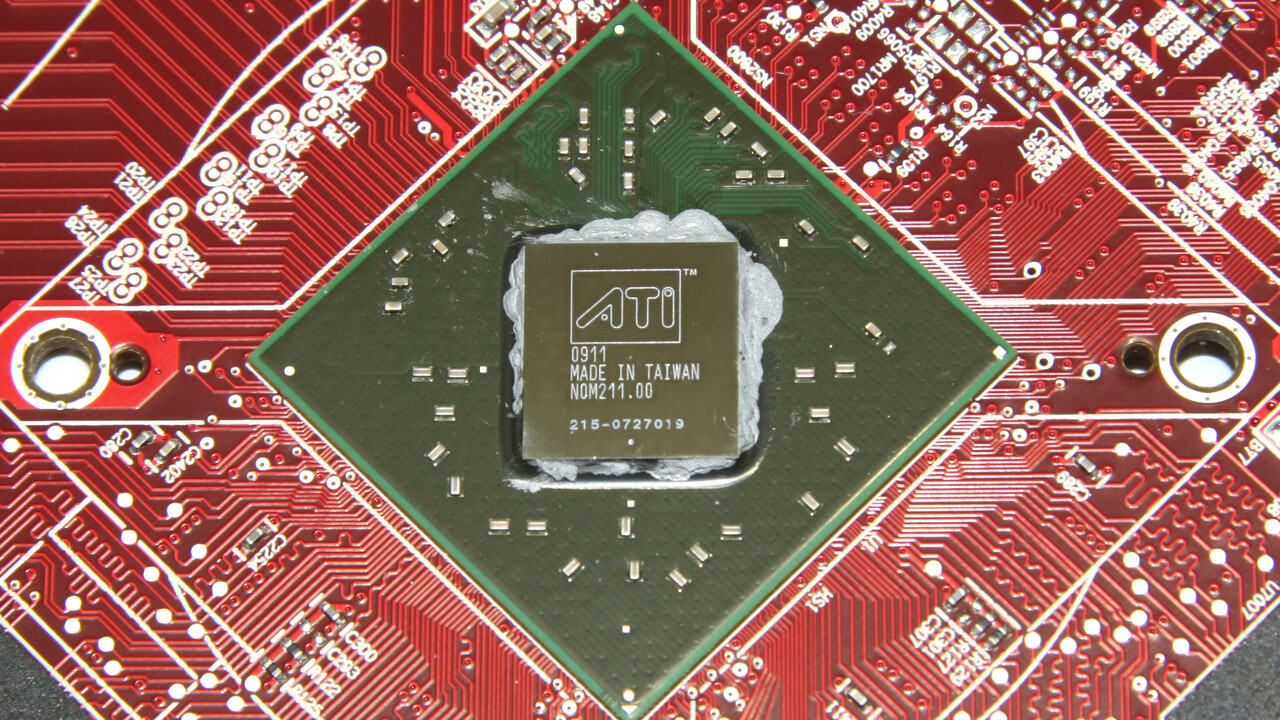
In testing 15 years ago: ATi Radeon HD 4770 impressed thanks to 40nm
A mysterious discovery on Mars – NASA team talks about “tire tracks” or “dragon scales”
iX Workshop: Passwordless authentication using passkeys, FIDO, SSO, and more