So-called WAP scams reserve premium services without the user’s knowledge. Billing by mobile phone bill. Users only have to give apps certain permissions like access to SMS.
Microsoft has analysis too The so-called toll fraud apps chest. These are scam apps for Android smartphones that use the built-in WAP functionality to trick users into subscribing to paid and mostly unwanted premium services.
According to software group researchers, the scam, also known as WAP fraud, is more complex than SMS fraud. However, malware that performs these multi-stage attacks is still among the most common forms of Android malware. The reason for this is that in many countries, premium WAP services are still automatically paid via the phone bill – users don’t have to agree to pay separately and usually only discover the premium subscription when checking their mobile bill.
Thus, the WAP scam malware is able to target users of some wireless service providers. Dynamic code loading, in turn, allows malware to hide its malicious functionality from security applications.
This type of malware usually only becomes active when the device is using some mobile service provider. According to Microsoft, they also only communicate via a cellular connection, even if a WLAN connection is available. The premium subscription booking page is then loaded in the background and the Subscribe button is clicked automatically.
Microsoft explained that “once you confirm connection to a target network, the malware secretly initiates and confirms a fraudulent subscription without user consent, and in some cases intercepts the one-time password (OTP) to do so.” Subsequently, SMS notifications for the subscription will be canceled to prevent the user from being aware of the fraudulent transaction and to opt out.
According to the analysis, such attacks are possible because Android apps can generally query the country code (mobile country code, MCC) and operator code (mobile network code, MNC) without the user’s consent.
Users can protect themselves from such malware by only getting apps from secret sources like Google Play Store. Microsoft also advises that some permissions, such as access to SMS features and accessibility, should not be granted easily.
Google is aware of the WAP fraud problem. In 2020, the company removed about 1,700 apps from the Play Store that contain variants of the Joker malware scam WAP.
In this country, the third party lock can be activated via the respective mobile phone provider – this generally prevents third party providers from being able to bill their services via the mobile phone bill. This is already preset at the factory by your mobile service provider Drillisch.

“Subtly charming coffee scholar. General zombie junkie. Introvert. Alcohol nerd. Travel lover. Twitter specialist. Freelance student.”






More Stories
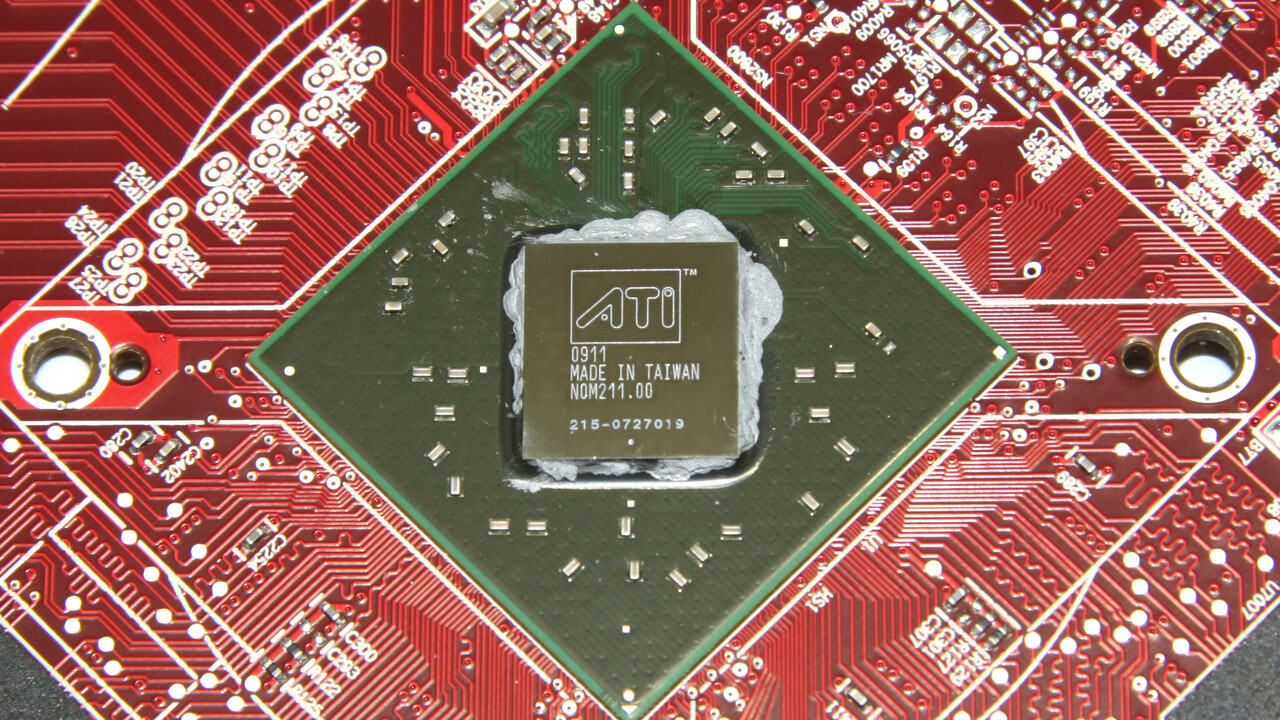
In testing 15 years ago: ATi Radeon HD 4770 impressed thanks to 40nm
A mysterious discovery on Mars – NASA team talks about “tire tracks” or “dragon scales”
iX Workshop: Passwordless authentication using passkeys, FIDO, SSO, and more